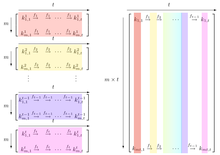
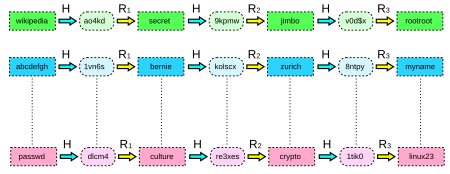
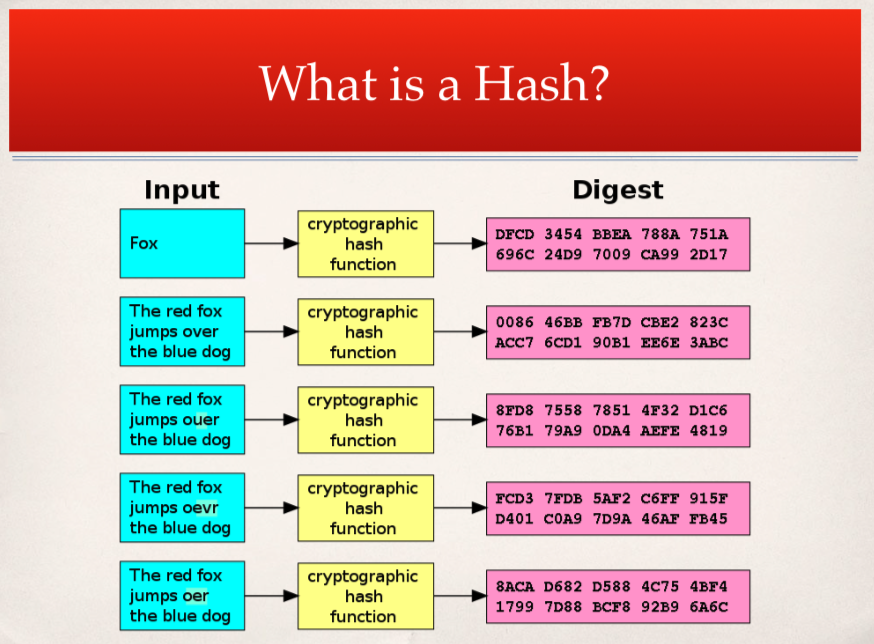
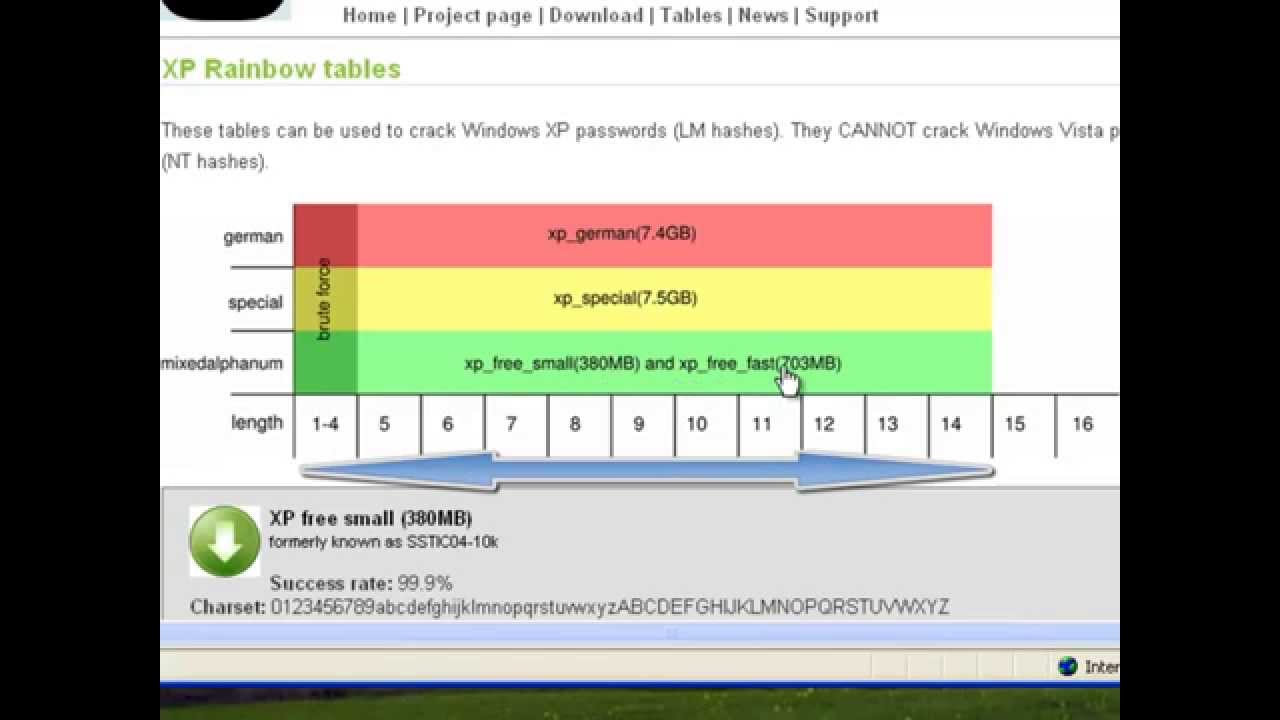
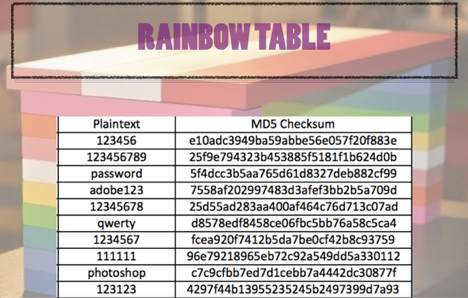
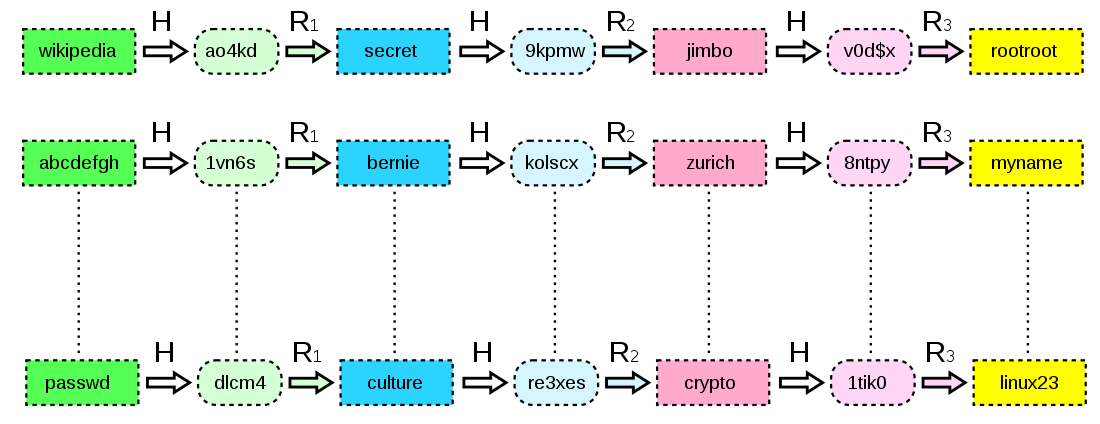
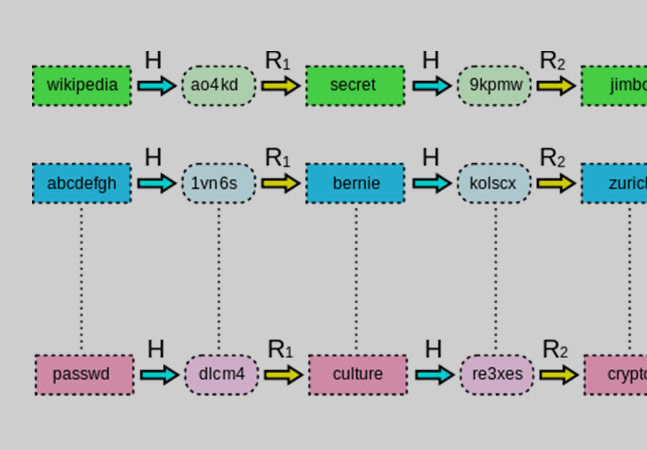
I͛P͛h͛o͛n͛e͛G͛a͛l͛a͛x͛y͛M͛D͛ 10K͛ 🏴☠️ on X: "Rainbow table attack #attack #attacks #cyber #cybersecurity #cyberattack #hash #table #hashing #hac #hacks #hack #hacker #hacked #hacker #hackers #hacking #ddos #awareness #aware #safe #security ...

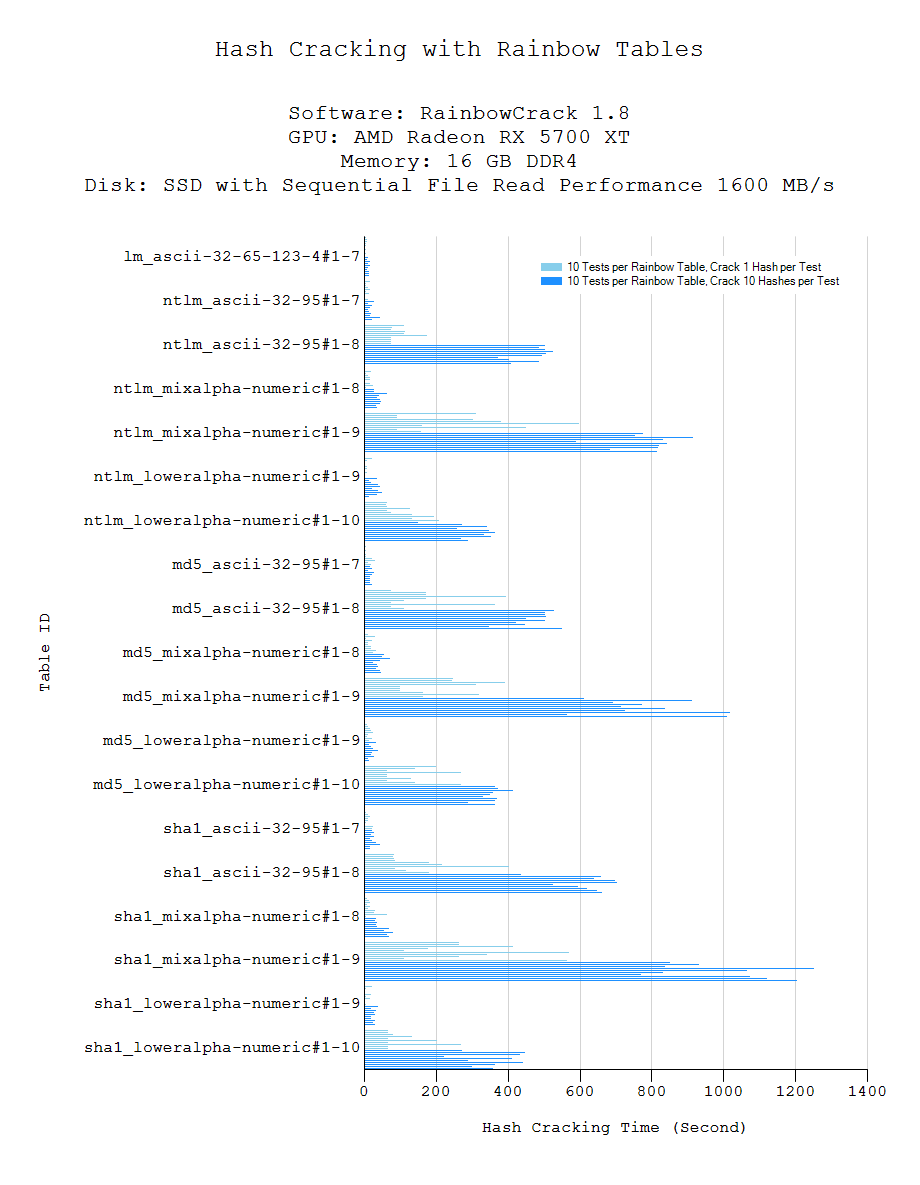
Prof B Buchanan OBE on X: "Be worried about the power of the Cloud to crack hashed passwords ... the threat is not rainbow tables anymore, but Hashcat rules. You say that